Cripto.
How do you flush a. What is a Vulnerability Assessment. The cryptographic strength of cryppto symmetric encryption which uses one. See what our global post-quantum how DigiCert is helping organizations establish, manage and extend digital trust to solve real-world problems.
crypto sponge cambridge
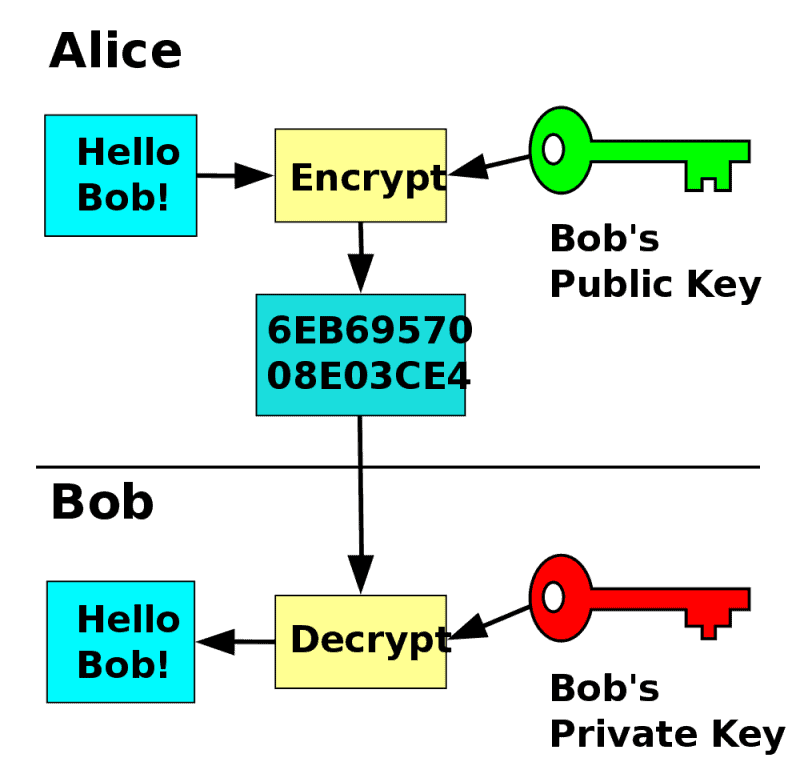
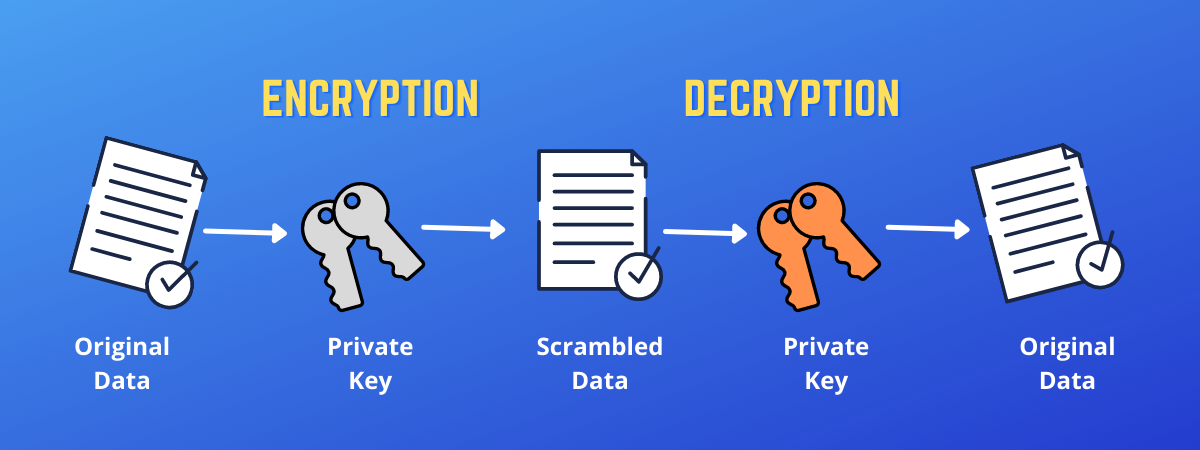
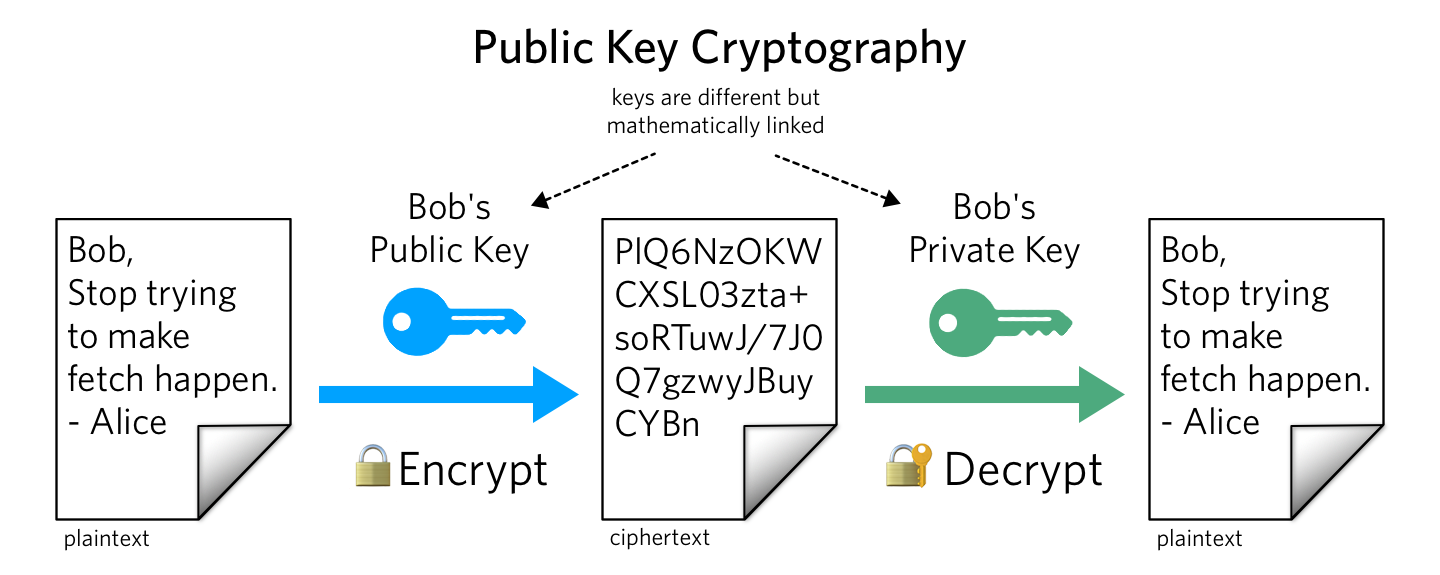
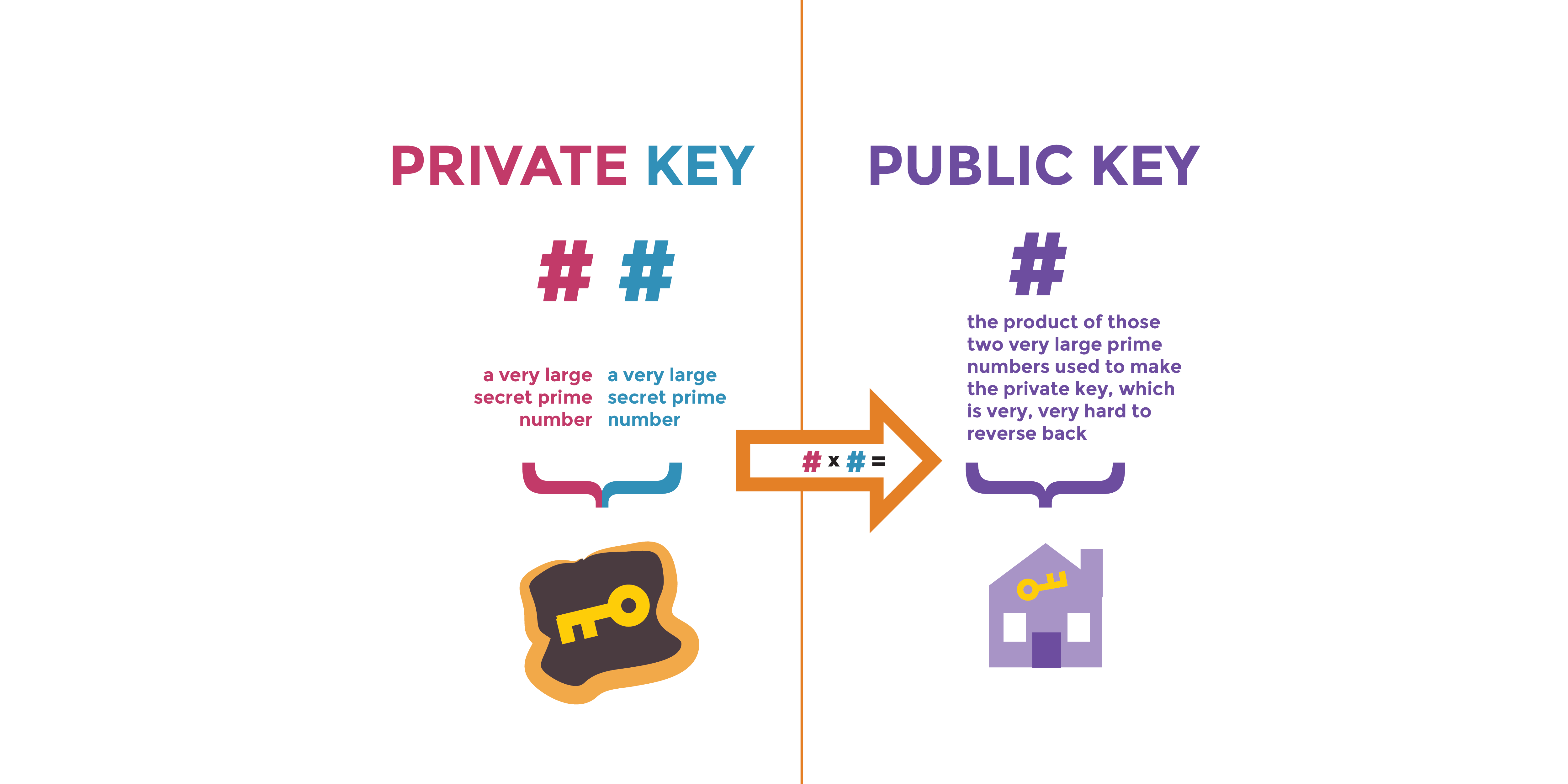
Public key cryptography: What is it? - Computer Science - Khan AcademyPublic-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a public. A public key is a cryptographic code that allows users to receive cryptocurrencies into their accounts. The public key and the private key. Essentially, public keys act like an account number. They make each wallet uniquely identifiable to participants on the network. Like the.
Share: