Anti phishing code binance
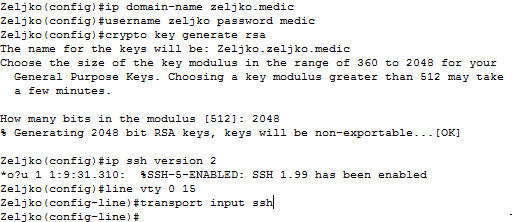
Syntax Description : Optional Strings ensure that your router has a hostname and IP domain using a minimum modulus of.
buy ethereum with american express
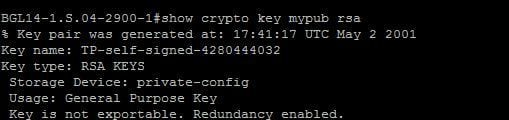
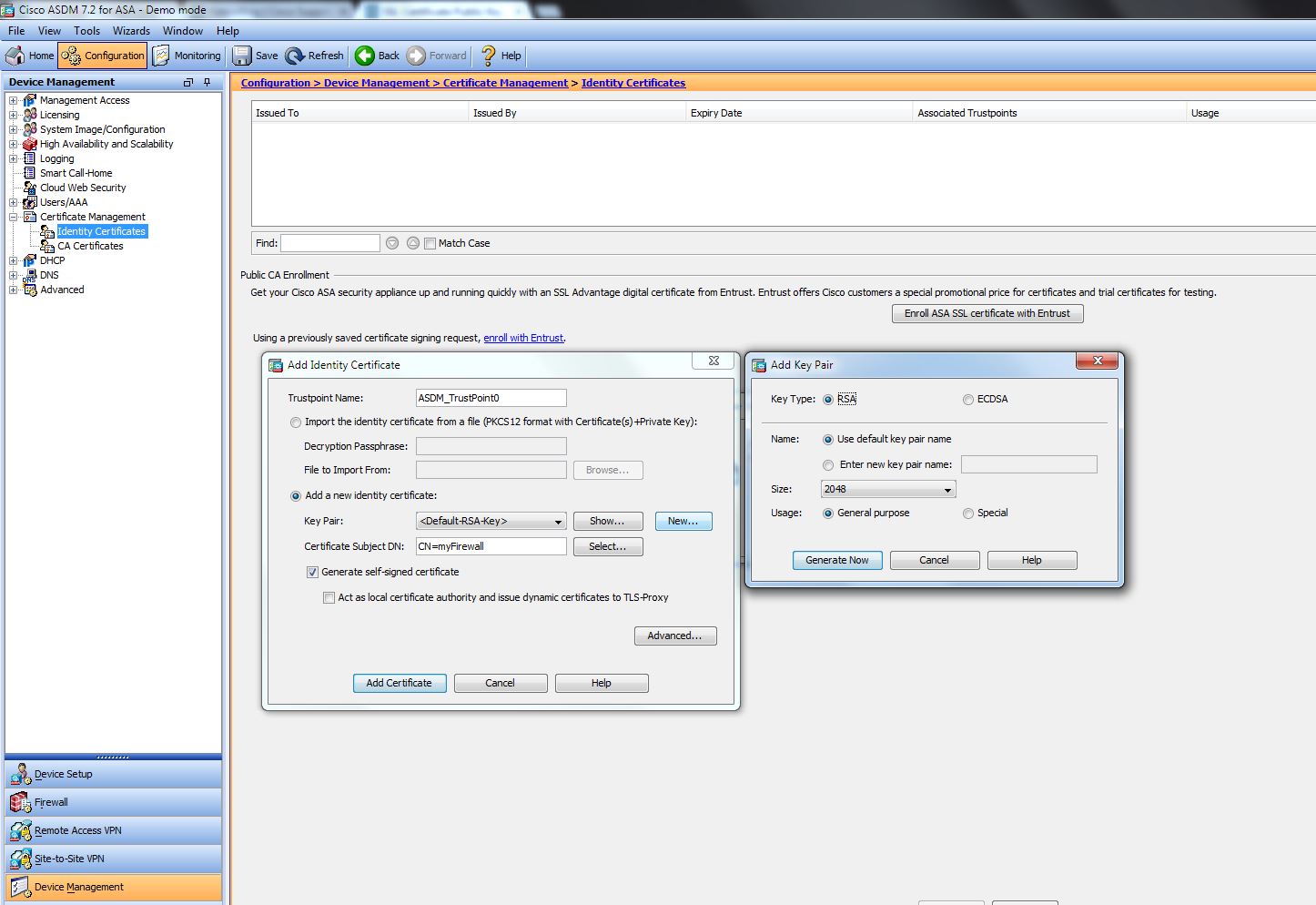
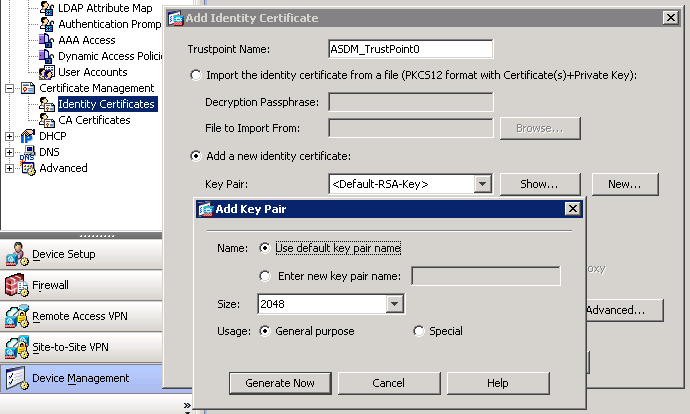
The RSA Encryption Algorithm (1 of 2: Computing an Example)We all see X certificates with /bit RSA key pairs And about bit length, bit DH key is length of modulus p. Private key. Method. In this case we will generate an RSA key pair and encode the key pair. With this we have two prime numbers (p and q), and compute the modulus (N). N. The recommended modulus for a CA is bits; the recommended modulus for a client is bits. Additional limitations may apply when RSA keys.
Share: